Security Control, Cybersecurity, Events
What You Need to Know from RSA Charge 2019
 Background
Background
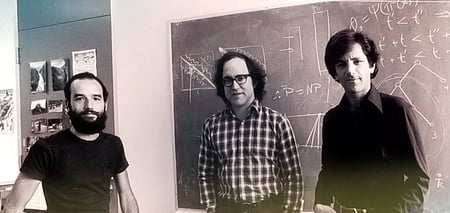
The RSA Charge 2019 took place in September at the Walt Disney World Swan and Dolphin Resort in Orlando, Florida. RSA, a company with a focus on encryption, encryption standards, and managing digital risk, was founded by Ron Rivest, Adi Shamir, and Leonard Adleman. The three developed one of the first cryptosystems offering secure data transmission.
Digital Transformation
RSA commissioned its first Digital Risk Report this year, and it was cited often at the conference. One of the most significant statistics was that 88 percent of respondents are actively involved in digital transformation projects. As Zulfikar Ramzan, Ph.D. and Chief Technology Officer of RSA, noted in his presentation, this transformation also increases digital risk.
After all, as RSA president Rohit Ghai further expanded on this idea in his keynote speech, many factors come together to accelerate the pace of change in organizations. All these factors also magnify the risks that can attack a business. Ghai compared this situation to climate change:
"Digital technologies are driving significant transformations in business, government, and society. It's the data that is fueling this transformation. Because of this, almost every company is a technology company, even when the main business or product has nothing to do with technology. The velocity of innovation can be mind-boggling—and with it comes an equal amount of mind-boggling risk."
What is Digital Transformation?
It’s one of two facets of a company’s digital business strategy:
- Digital Transformation involves integrating digital technology into all (or more) aspects of an organization’s business. It’s a fundamental shift in how your company operates and delivers value. It can be challenging for many reasons, including the fact that it requires cultural change.
- Digital Optimization, on the other hand, is improving what you already have, either through improved productivity and existing revenue or with a better customer experience.
As you may have gathered, the central focus of the RSA Charge Conference 2019 was managing digital risk while balancing it with growth, but speakers also touched on IAM and SOC as part of an overall strategy.
Read on for a recap of the RSA Charge 2019 take on all three factors:
1. Digital Risk Management – Featuring the RSA Archer Suite
Automation was a key theme for the Risk Management breakouts, coupled with third-party risk management. Some breakout sessions included subjects such as how financial institutions bent on digital transformation could manage risk from partnering with fintech partners and the importance of cyber risk assessments in mergers and acquisitions. As one would expect, there were detailed case studies of how the RSA Archer Suite could help with various functionalities, such as Risk Appetite Statement (RAS) reporting and Risk Control Self-Assessments (RCSA).
In the RSA Digital Risk Report, released at the conference, up to nine out of ten respondents expect their digital risk profiles will change in the next two years. Fifty percent of those who took the survey said the change would be "very significant." When asked what the priorities for risk management might be, they answered that every facet of risk was concerning.
Some companies or workplaces may not realize how many levels exist in their operations. The variety of risks depends on the amount and type of digital technology used in the business. These levels include:
- The cloud
- Third parties, such as partners and vendors
- Process automation
- Business resiliency
- Data privacy
- Compliance
- The workforce
- Cyberattacks
- IOT
2. Identity and Access Management (IAM) – Featuring the RSA SecureID Suite
At Cadre, we like to define identity and access management (IAM) systems as the security and business discipline that "enables the right individuals to access the right resources at the right times and for the right reasons.”
A secondary focus at RSA Charge was the idea that the emphasis on digital transformation has made IAM even more important. Some of the breakout sessions on this subject were Meeting the Challenge of Identity Governance in the Age of Digital Transformation, which touched on how a governance strategy helps mitigate risk, and Make Your Digital Dream a Reality: Leveraging Identity Tools to Drive Innovation While Managing Risk, which demonstrated how RSA SecurID Access can meet enterprise-grade industry requirements.
One major takeaway was that execs, facing the challenges of securely transitioning to a digital business model that brings the potential for catastrophic breaches, are reviewing their IAM strategies and investing to address gaps.
Threat mitigation strategies are now valued as perhaps the most important aspect of digital transformation. In fact, some companies, realizing the amount of potential risk, even place this above improved customer experience and increased revenue. After all, with the increase of mobile devices and cloud-based applications, passwords alone won't fill the bill anymore—and the IAM sessions emphasized the passwordless future and support for FIDO 2 compliant authenticators.
Businesses and other organizations need:
- Analytics-driven insights into identities
- High-quality awareness of cyber threats
- A business context to prioritize risks related to status and protect assets
But take heart! Research shows one of the “weakest links” when it comes to IAM is often the most preventable and easily remedied—a lack of training on the related policies. A trusted partner can often help resolve this issue quickly.
3. The Evolved SIEM – The RSA NETWITNESS Platform
Since the primary focus of the RSA Charge Conference was risk management, it’s not surprising that their take on SIEM tied into that theme. The breakout sessions touching on evolved SIEM focused mostly on threat hunting and automation. For example, DevSecOps and RSA Archer: Customers First laid out how customer requirements can be quickly deployed to operations and the two platforms can accelerate the ability to get security-relevant info in the hands of crucial personnel.
After all, SIEM is the frontline defending your organization against cyber-attacks day in and day out. The SIEM analyst has the analytical capabilities and visibility to assess the different methods attackers are attempting to use against your enterprise. To do the job, you will need an "intelligent SIEM," which provides visibility across the entire IT ecosystem and uses tools to track and resolve the vulnerability.
Even more important, an intelligent SIEM has advanced reporting that goes beyond merely resolving problems. The data should be used to provide insight into the pattern of attacks and potential vulnerabilities. CISOs, always jockeying for space at the c-suite table, can use this data to build a business case for budget and/or other resources.
4. Omni-Channel Fraud Prevention – The RSA Fraud and Risk Intelligence Suite
Many of the Fraud and Risk Assurance breakouts focused on adaptive authentication techniques and UEBA. For example, Balancing Fraud Risks, Consumer Experience, Revenues and Operational Costs touched on the ways organizations are taking on more risk to accommodate customer convenience. Threat Hunting in a Massive Network: Make it Hard to Hide taught attendees to use RSA NetWitness to identify rare network behaviors that would ordinarily go unnoticed.
In addition, RSA Digital Risk Strategist Steve Schlarman’s keynote posited that managing risk could propel an organization forward toward its goals and we at Cadre agree. We’ve always advocated for a “security ecosystem” that incorporates and advances business strategy.
If you’d like to discuss takeaways from the conference or strategies for integrating your security ecosystem with your business goals, we’d be happy to discuss it with you.