Cybersecurity,Security Awareness,Internet of Things,multifactor authentication,MFA
Authentication vs. Privacy
Like many “teeter-totter” issues, there is a give-take relationship between new authentication...
Read more
Security Awareness
Cybersecurity Awareness Q&A
To celebrate Cybersecurity Awareness Month this year, Laurie Mason interviewed Tim O'Connor, CISO &...
Read more
Cyber Threats,Security Awareness,chatgpt
ChatGPT: A Boon to Scammers
Me: write me a phishing email ChatGPT: Me: You are an IT manager. Write an email to your finance...
Read more
Security Awareness
New Scam Alert + Easy to Share Information for Employees
For Security Awareness to be effective, it has to be a continuous effort based on current threats....
Read more
Security Awareness,multifactor authentication
Why ‘Enable MFA’ is Lousy Advice
This year’s Cybersecurity Awareness Month Theme – “See Yourself in Cyber” – offers four actionable...
Read more
Security Awareness,multifactor authentication,MFA
4 Things a Data-Driven Defense Evangelist Wants You to Know
This year’s Cybersecurity Awareness Month theme is “See Yourself in Cyber” – highlighting the...
Read more
Cybersecurity,Security,Security Awareness
Is this Critical Mistake Hurting Your Cybersecurity Risk Posture?
One of the great ironies of IT is that so many IT and security departments are built on two basic...
Read more
Security Awareness
The Biggest Security Awareness Misconceptions – Part 1
There’s a conversation that has been playing on repeat about Security Awareness. It usually goes...
Read more
Security Awareness
NEW PODCAST: Security Awareness is More Than Just Phishing Training
Security Awareness is a critical tool in an organization's toolkit. Yet, it tends to be a lower...
Read more
Security Awareness
Minimize Security Incidents with a Strong Security Awareness Program
News of companies getting hacked is omnipresent. The fear, uncertainty, and doubt as a result of...
Read more
Security Awareness
How to Develop an Effective Security Awareness Program
Security Awareness is well known for being the “best bang for the buck” out of all the risk...
Read more
Security Awareness
The Worst Things to Share on Social Media
As a business professional, why should you care what your employees post on social media? Even...
Read more
Security Awareness,smartphone security
The Latest Smart Phone Hacking Update
New security concern: Malware that can copy all the physical keys on your keychain!
Read more
Security Awareness,vciso
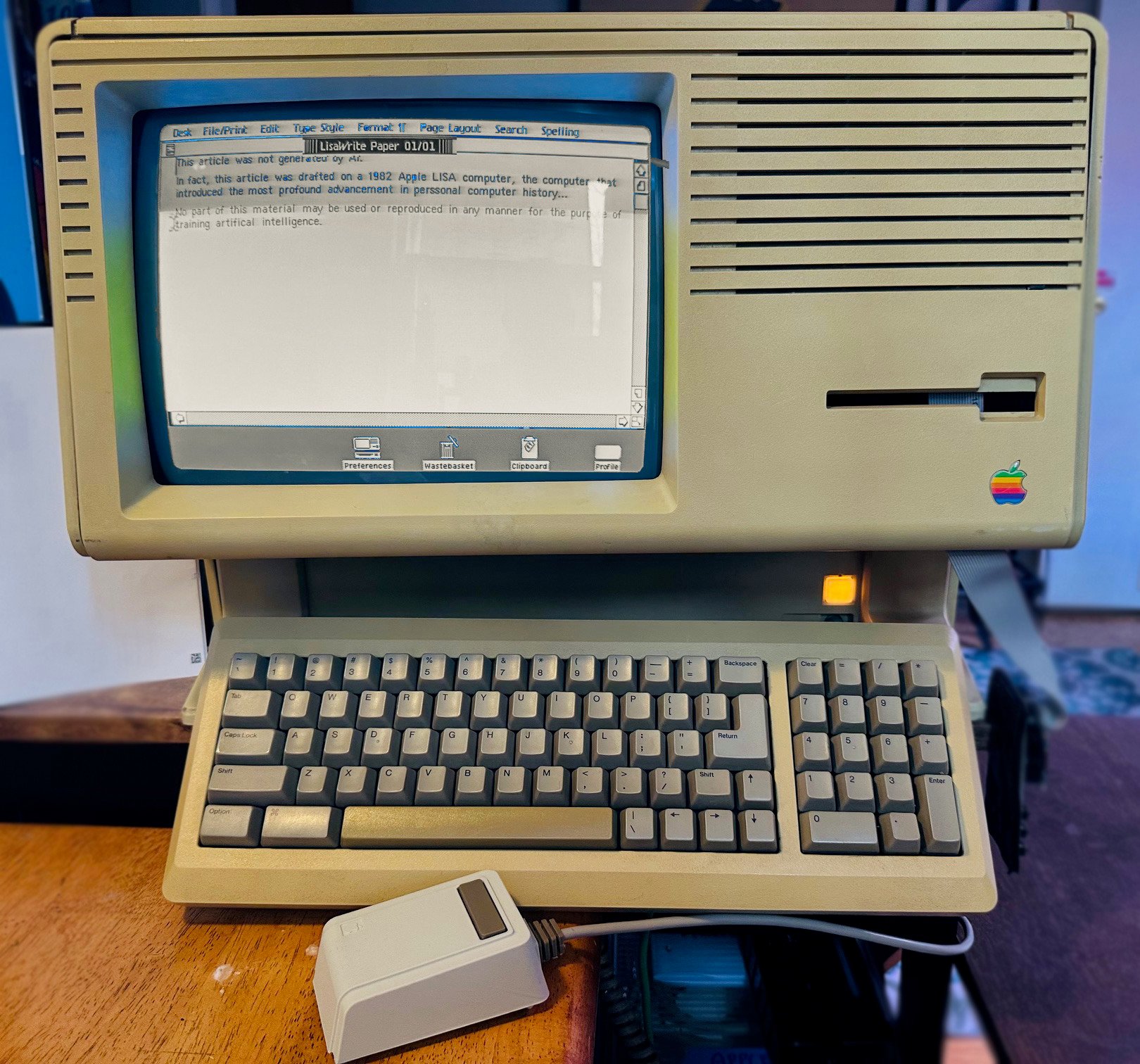
Winning Bug Wars: From Volkswagen Beetles to Million Dollar Bug Bounties
Bugs have been wreaking havoc in humanity long before the rise of information technology, but the...
Read more
Vulnerabilities,Cybersecurity,Cyber Threats,Security,Security Awareness
A Pen Testing Expert Shares the Secret Ways He Gains Access to Businesses
Steve Stasiukonis’ company, Secure Network Technologies, does all kinds of pen testing. When we say...
Read more
Vulnerabilities,Cyber Threats,Security,Security Awareness
The Biggest Threats to Businesses from a Pen Testing Expert
Steve Stasiukonis started doing pen testing professionally in 1997, when a former classmate of his...
Read more
Vulnerabilities,Security Awareness,remote work
Best Practices When Trying to Protect Your Information While Working Remotely
Asaf Lerner’s work in the identity and access management (IAM) space has spanned 20 years and two...
Read more
Cybersecurity,Security Awareness
How to Enable Your Employees to Work Remotely Without Compromising Security
With the current economic and social uncertainty in today’s landscape and the rush to transition...
Read more
Security Awareness,remote work
How to Transition to Working Remotely During a Crisis
Jim Hebler has worked in cybersecurity for nearly 18 years. He started out covering technology as a...
Read more
Cyber Threats,Security,Security Awareness,remote work
Little-known Facts About Remote Worker Security that Could Damage Your Business
With the ongoing rush to transition staff to remote workers, great opportunities open for con...
Read more
Cybersecurity,Cyber Threats,Security Awareness
Five Tips to Ensure Your Company's Bluetooth Security Policies are Up to Date
Urban Legend Becomes Real Several years ago some reports came to information security experts from...
Read more
Vulnerabilities,Cybersecurity,Security,Security Awareness
5 Cyber Security Recaps from the Past Decade—And 5 Predictions for the Next One
While there's a heated debate about whether a new decade is actually beginning, the beginning of a...
Read more
Vulnerabilities,Security Control,Security Awareness
When the Next Recession Comes, Will Your Security be Ready?
Recessions stink. Business contracts, companies pull back and attempt to shrink inventories,...
Read more
Security Control,Cybersecurity,Security Awareness
The Fact and Fiction of the Business Risks Posed by IOT Devices
A casino hacked through an aquarium heater* sounds like fiction—but this recent headline news was...
Read more
Cybersecurity,Cyber Threats,Security Awareness
How to Prevent 4 Network Security Threats that Cost Financial Services Millions
The Capital One breach exposed over 100 million customers’ sensitive information. In 2017, 147.9...
Read more
Cybersecurity,Cyber Threats,Security Awareness
Myth Busted: Small Organizations are at Low Risk of Hacking Because they are not Desirable Targets For Hackers
All of these are common myths, but only one has dangerous misinformation. Can you figure it out?...
Read more
Cybersecurity,Cyber Threats,Security,Security Awareness
A Former CTO of the FBI Cyber Division on the State of Cybersecurity
Part 3 of a three-part series Milan Patel, current chief client officer at BlueVoyant and former...
Read more
Security,Security Awareness
9 Questions You Should Ask When Considering Cloud-Based Tech
To paraphrase Zoolander, cloud-based technology is so hot right now. There are good reasons for...
Read more
Cybersecurity,Cyber Threats,Security,Security Awareness
How to Improve Your IT Security for the Upcoming Elections
Small governments seem to be stuck between a rock and several hard places.
Read more
Cybersecurity,Security,Security Awareness
New Tools to Protect Credit Cards at Gas Stations But Who Gets to Use Them?
If you live in the U.S. and have ever noticed false charges on your credit card statement and had...
Read more
Cyber Threats,Security,Security Awareness
If Your Healthcare Data is Leaked Chances are Your Doctor’s Office, not an Evil Hacker, is to Blame
New research from Michigan State and Johns Hopkins Universities show that failed internal...
Read more
Cybersecurity,Security,Security Awareness
New Advances Show Evil Hackers can use Cell Phone Apps to Capture your Information by Sound
Evil hackers and corporate spies have had the ability to record the loud tap-tap-tap of computer...
Read more
Vulnerabilities,Security Control,Security,Security Awareness
5 Mistakes Made In the Capital One Breach and How to Avoid Them
If an amateur hacker could bring down a Fortune 500 company, how can your company hope to avoid the...
Read more
Security,Security Awareness
What Data Breaches and the Notre Dame Cathedral Fire Have in Common
On April 15, 2019, a flame ignited Notre Dame Cathedral in Paris and many watched as roughly 500...
Read more
Vulnerabilities,Cybersecurity,Security,Security Awareness
5 Lesser Known Impacts of Poor Security
You wouldn’t leave the doors to your business unlocked, would you? Of course you wouldn’t. In the...
Read more
Vulnerabilities,Security Control,Cybersecurity,Security Awareness
Security Trends and Takeaways for the Second Half of 2019
So much has happened in terms of information security and breaches in 2018 that it can be a little...
Read more
Security,Security Awareness
5 Ways to be Sure You’re not Over- or Under-Solving for Security
Remember the story of Goldilocks breaking into the three bears’ cottage and wreaking havoc?...
Read more
Cyber Threats,Security Awareness
Grab-n-Go Baldr Malware: A Stunning New Type of Malware
A revolutionary new type of malware toolset is starting to show up in dark web hacking forums. The...
Read more
Security,Security Awareness
Why the Citrix Breach Happened and 6 Steps You Can Take to Protect Your Company
What happened? Citrix, an American software company, disclosed a security breach in which hackers...
Read more
Security Awareness
Security Awareness Training FAQs
We receive a number of questions regarding security awareness training. Below are some common...
Read more
Security Awareness
5 Things to keep in mind when Implementing a Security Awareness Program
What are the 5 most important things to keep in mind when implementing a security awareness...
Read more
Security Awareness
Cadre’s Security Awareness Services Meet Requirements for Major Compliance Standards
Cadre’s Security Awareness class, course design and consulting services are now able to meet...
Read more
Security Awareness
How to Create an Effective Security Awareness Program
"Social engineering bypasses all technologies, including firewalls." -Kevin Mitnick Social...
Read more
Security Awareness
How to Legally Practice Social Engineering
Social Engineering is without question the most powerful and successful hacker skill of all time,...
Read more
Security Awareness
Should we Fear the Amazon Echo or Other Smart Speakers in our Home?
Author: Tim O’Connor I am a cyber security professional and when I tell some of my peers that I...
Read more
Security Awareness
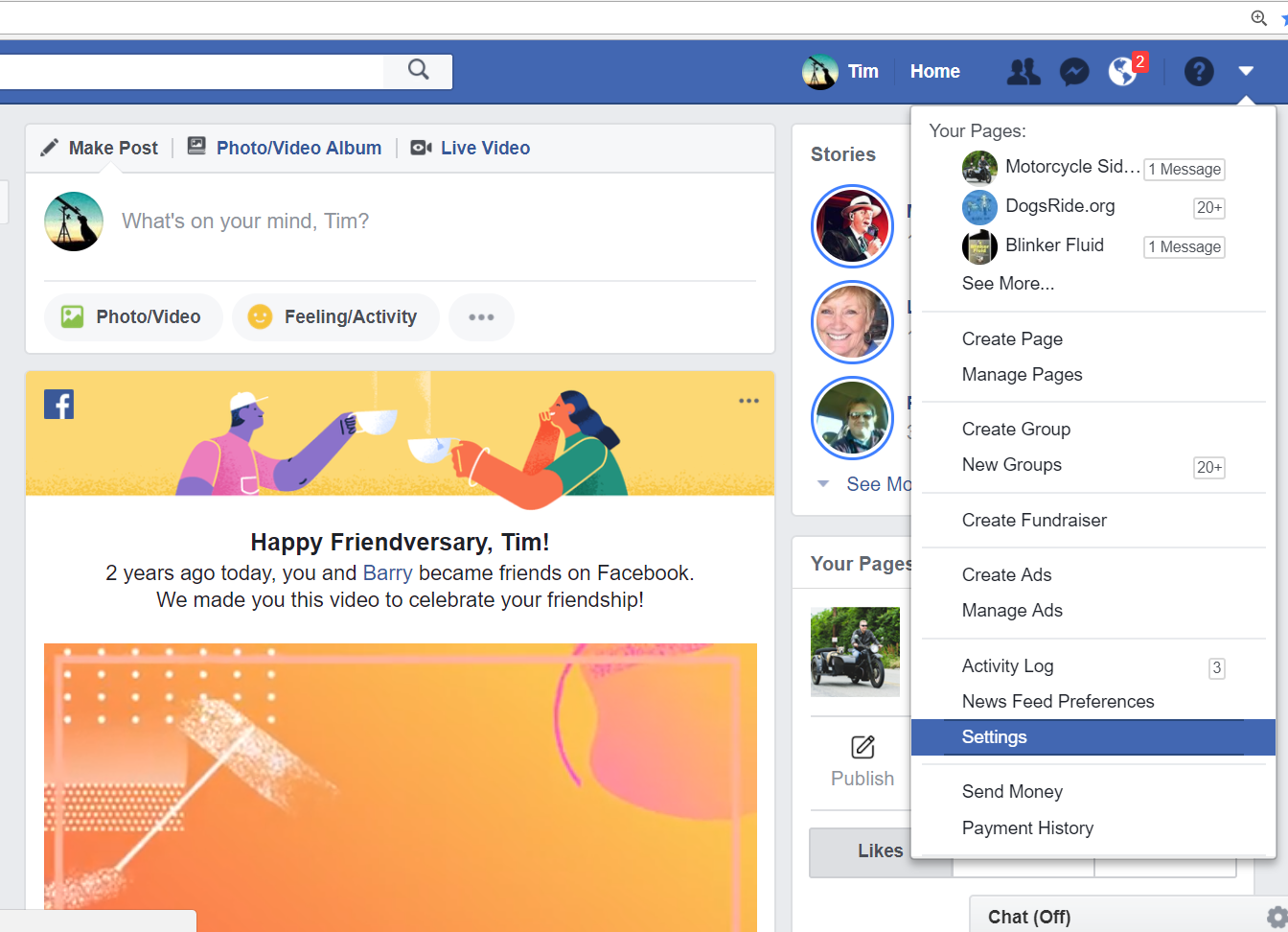
Don't Lose Face with your Friends over Facebook
Author: Tim O'Connor You have likely been hearing about the personal privacy leakage court cases...
Read more
Security Awareness
Security Awareness Evaluation - Don't Fall for the "Streetlight Effect!"
A policeman sees a drunk man searching for something under a streetlight and asks what the drunk...
Read more