Vulnerabilities,Cyber Threats
Iran vs. U.S. Mid-Market Enterprises: Why You Can’t Afford to Sit Out Conflict
The news cycle moves at lightning speed. We see headlines like, “Amazon’s cloud business in Bahrain...
Read more
Why Automation and Cyber Risk Transfer Must Evolve Together
AI is no longer experimental. According to the 2026 Software Lifecycle Engineering Decision Maker...
Read more
Authorized Check Point Training Center Offering R82 and R81.20 Courses
As an Authorized Check Point Training Center, Cadre offers instructor-led, hands-on certification...
Read more
Step Back in Time: Tim O’Connor’s Vintage Hacking Demos at Queen City Con
Get ready to explore the roots of computing and hacking history at Queen City Con, November 7-9!...
Read more
Our Newest Technology Partners: Empowering Your Security and IT Strategy
At Cadre, we constantly seek innovative and effective solutions to support our customers’ evolving...
Read more
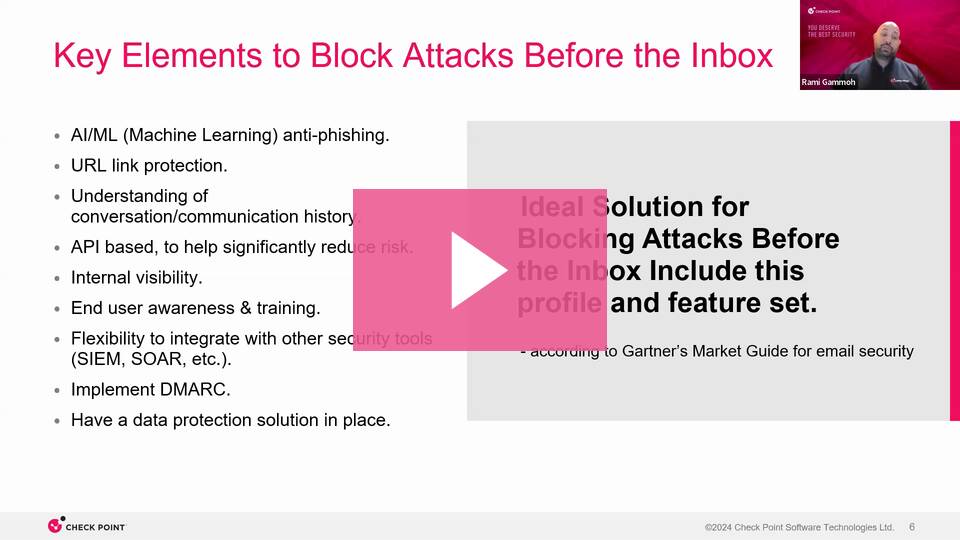
How to Block Attacks 'Before' the Inbox
On Wednesday, October 23, 2024, we hosted a webinar with Check Point Software to discuss how...
Read more
Security Awareness
Cybersecurity Awareness Q&A
To celebrate Cybersecurity Awareness Month this year, Laurie Mason interviewed Tim O'Connor, CISO &...
Read more
Email Compromise Remains Top Threat Incident Type for the Third Quarter in a Row
New analysis of Q2 threats shows a consistent pattern of behavior on the part of threat actors and...
Read more
Ransomware
The Evolution and Future of Ransomware
Previously posted on KnowBe4.com by Javvad Malik The history of ransomware spans over 30 years. The...
Read more
Cadre Now Available on AWS Marketplace
We are thrilled to announce that Cadre Information Security is now on the AWS Marketplace. Today,...
Read more
iot,Ransomware,Higher Education
Rising Threats: 2024 Cybersecurity Trends Impacting Higher Education
Nearly two-thirds of campus leaders ranked data security as one of their top concerns. This comes...
Read more
Events
March Events: CPX, happy hour, golf, and more!
The team here at Cadre is excited for another year filled with fun and educational events. Check...
Read more
Top 3 Cloud Security Risks for Higher Education
Colleges and universities are top targets for cyberattacks, from malware to ransomware to data...
Read more
Security,Secure Access Service Edge,sse
Should You Consolidate Security to Protect Your Hybrid Workforce?
In today's fast-changing world of hybrid networks and workforces, companies are at a pivotal moment...
Read more
The Evolving Role of Generative AI as a Cybersecurity Force Multiplier
Nine months ago, the conversations about generative AI were limited. Now, it’s all everyone wants...
Read more
2023 Ransomware Statistics Roundup
The chatter around ransomware makes most people want to do one of two things:
Read more
Ransomware
Q&A: Defense-in-Depth Strategies for Ransomware Threats
In our latest webinar, Defense-in-Depth Strategies for Ransomware Threats, we received so many...
Read more
Cyber Threats,Security Awareness,chatgpt
ChatGPT: A Boon to Scammers
Me: write me a phishing email ChatGPT: Me: You are an IT manager. Write an email to your finance...
Read more
Top 5 Security Must-Haves to Fight Ransomware
The high incidence of ransomware isn’t an issue swept under the rug these days. It’s glaringly...
Read more
Upcoming Events You Won’t Want to Miss
The team here at Cadre is excited for another year filled with fun and educational events. Check...
Read more
Cybersecurity
Managing Cybersecurity Through the Economic Downturn
Consider the economic downturn as part of a cyclical process. It puts everything in a better...
Read more
sse
Security Service Edge (SSE) empowers you to say YES and stay secure
Saying ‘no’ all the time isn’t fun for the security team, and it certainly isn’t enjoyable for...
Read more
Security Awareness,multifactor authentication
Why ‘Enable MFA’ is Lousy Advice
This year’s Cybersecurity Awareness Month Theme – “See Yourself in Cyber” – offers four actionable...
Read more
Security Awareness,multifactor authentication,MFA
4 Things a Data-Driven Defense Evangelist Wants You to Know
This year’s Cybersecurity Awareness Month theme is “See Yourself in Cyber” – highlighting the...
Read more
cyber insurance
NEW PODCAST: The Current State of Cyber Insurance in 2022
As ransomware and other cyber threats grow, it has become increasingly difficult to find and...
Read more
cybersecurity insurance,cyber insurance
How to Reduce Your Cyber Insurance Premiums
Ransomware increased by almost 13% – a rise as big as the last five years combined (for a total of...
Read more
SANS Survey 2022: Securing Infrastructure Operations
For organizations that want to quickly scale to meet operational and/or customer needs, a cloud...
Read more
Security Ratings: A Smart Choice to Kick off the New Year
For many people, with the new year comes goals, resolutions, and a general sense to ‘do better’...
Read more
Security
2022 Cyber Security Predictions
2021 has been quite the year with the latest Log4j vulnerability as the cherry on top. Our...
Read more
Security Awareness
NEW PODCAST: Security Awareness is More Than Just Phishing Training
Security Awareness is a critical tool in an organization's toolkit. Yet, it tends to be a lower...
Read more
Cybersecurity
10 Cybersecurity Best Practices for Mid-Size Organizations
Alleviating cybersecurity risks comes in many shapes and sizes—and so do organizations. Large...
Read more
Events
You Won't Want to Miss This: Upcoming Events 2021
The Cadre team is excited to announce we will be hitting the road (and online) to safely connect...
Read more
Security
Meet XDR: A New Approach to Threat Detection and Response
You’ve probably heard about it. Maybe you wrote it off as just another product on your...
Read more
solarwinds attack
The SolarWinds Breach: What Your Business Can Learn From It
The SolarWinds compromise continues to stun government agencies and enterprises across industries...
Read more
Secure Access Service Edge,SASE
Secure Access Service Edge (SASE): Getting Sassy in the Cloud
Operating on the edge with vigorous due diligence Moving business processes, applications, and data...
Read more
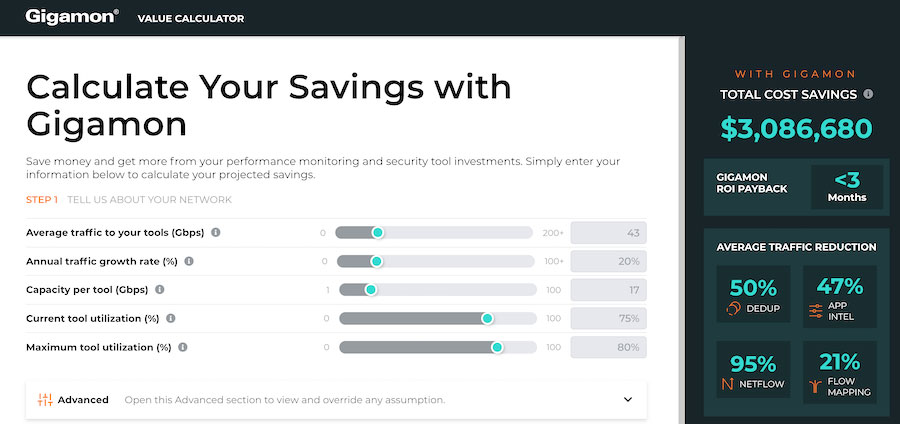
IT Budget,Gigamon
IT Budget on Hold? Gigamon Saves Big — and Pays for Itself
You’re about to push the button on a big investment. You’ve done all the recommended planning and...
Read more
The Current State of Security for the Internet of Things
The production industry has seen incredible changes over the last few centuries, and while emerging...
Read more
Security Awareness,vciso
Winning Bug Wars: From Volkswagen Beetles to Million Dollar Bug Bounties
Bugs have been wreaking havoc in humanity long before the rise of information technology, but the...
Read more
active directory
7 Tips for Proactively Using Active Directory
Active directory is currently the most popular directory because it is proprietary to Microsoft...
Read more
Security Control,Cybersecurity,Cyber Threats,Security
Five Critical Steps for an Effective Remote Training Strategy
Cybercrime has skyrocketed during the pandemic, as untrained remote workers adapt to new...
Read more
Vulnerabilities,Cybersecurity,Security
Reopening After COVID-19: Looking Back and Strategies Moving Forward
Businesses are eager to open their doors, many remote workers are ecstatic about it, but reopening...
Read more
Vulnerabilities,Security Awareness,remote work
Best Practices When Trying to Protect Your Information While Working Remotely
Asaf Lerner’s work in the identity and access management (IAM) space has spanned 20 years and two...
Read more
Events
Join us for Happy Hour in Cincinnati
We are kicking off 2020 with our first Serve and Protect event in Cincinnati, OH on March 4th! If...
Read more
Vulnerabilities,Cybersecurity,Security,Security Awareness
5 Cyber Security Recaps from the Past Decade—And 5 Predictions for the Next One
While there's a heated debate about whether a new decade is actually beginning, the beginning of a...
Read more
Security Control,Cybersecurity,Security
5 Factors to Make Your Secure Cloud Migration a Success
As more businesses transition their infrastructure to the cloud, understanding how to securely...
Read more
Security Control,Cybersecurity,Events
What You Need to Know from RSA Charge 2019
Background The RSA Charge 2019 took place in September at the Walt Disney World Swan and Dolphin...
Read more
Security Control,Cybersecurity,Security
10 Reasons a vCISO May Be a Good Choice for Your Company
If your company is like most, you’ve grappled with the high cost of a Chief Information Security...
Read more
Security Control,Cybersecurity,Security
SOAR in the Cloud: 7 Factors to Consider
As cybercrime increases, it’s impossible for employees to keep up with every threat. It’s crucial...
Read more
Cybersecurity,Cyber Threats,Security Awareness
How to Prevent 4 Network Security Threats that Cost Financial Services Millions
The Capital One breach exposed over 100 million customers’ sensitive information. In 2017, 147.9...
Read more