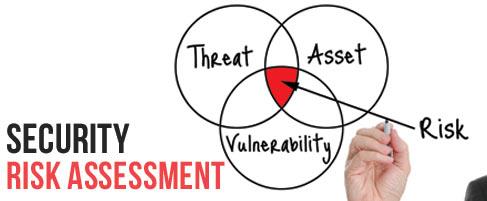
What to Do After a Security Risk Assessment
As the person responsible for cybersecurity risk, you knew it was time to identify and modify your...
Read more
Security Awareness
Minimize Security Incidents with a Strong Security Awareness Program
News of companies getting hacked is omnipresent. The fear, uncertainty, and doubt as a result of...
Read more
penetration testing
What Are The Different Types of Pen Testing?
The news these days is filled with stories of data breaches, hacks and (gasp) ransomware. And we’ve...
Read more