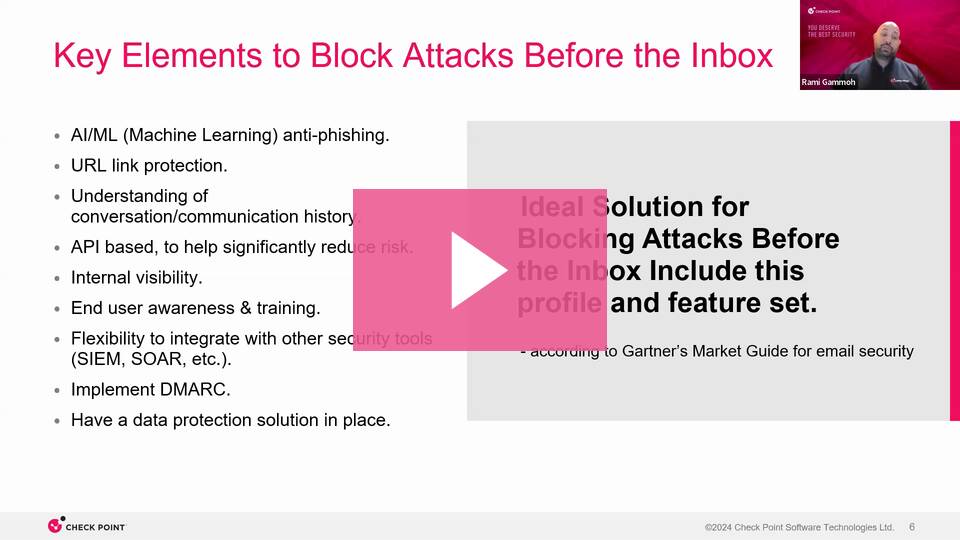
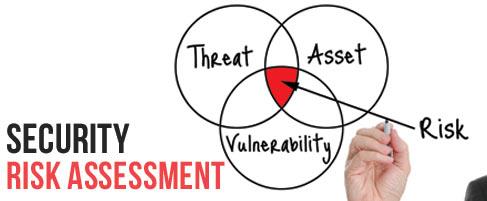
Vulnerabilities,Cyber Threats
Iran vs. U.S. Mid-Market Enterprises: Why You Can’t Afford to Sit Out Conflict
The news cycle moves at lightning speed. We see headlines like, “Amazon’s cloud business in Bahrain damaged in Iran strike,” ...
Read more




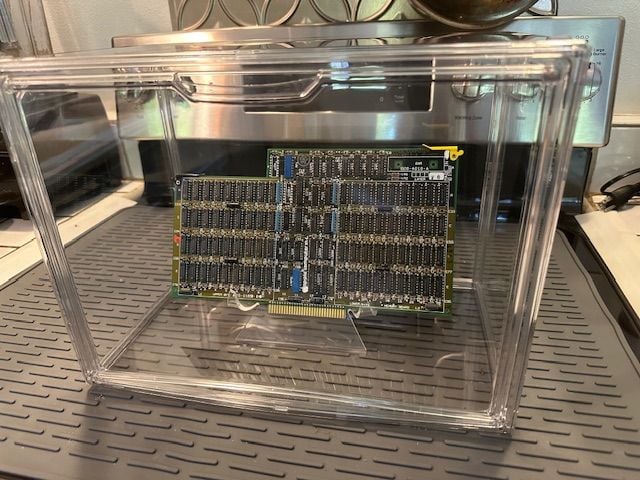
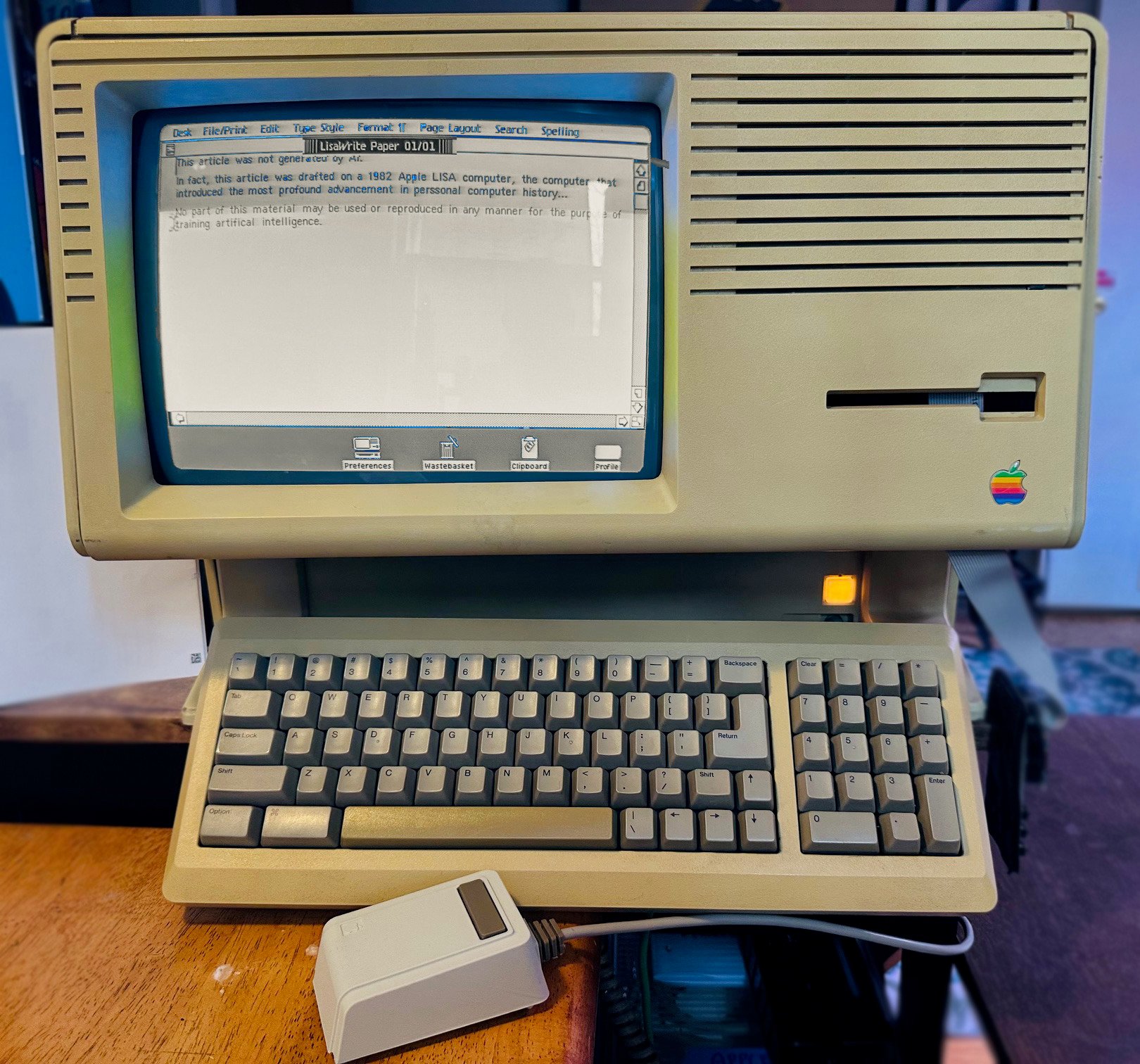
.jpg)